The simple story is this: a person walks up to a checkpoint, counter, kiosk, or app flow with a mobile ID on their phone, and Credence ID provides the verifier in the form factor that fits the deployment. Tap2iD Verifier is the hardware version, Tap2iD SDK is the software version, and Verify with Credence is the web portal used to configure devices, manage trust settings, and monitor deployments. The Triangle of Trust explains why the result can be trusted.
01
The in-person verification story in plain language
✅
What each product does
A business needs to verify someone standing in front of it. If it wants a purpose-built reader, it uses Tap2iD Verifier. If it wants to add that same mDL verification capability into its own Windows, iOS, or Android workflow, it uses Tap2iD SDK. If it wants to manage configuration, monitoring, and compliance data centrally, it uses Verify with Credence. The user experience stays simple: tap, share, and verify.
02
Why that verification can be trusted
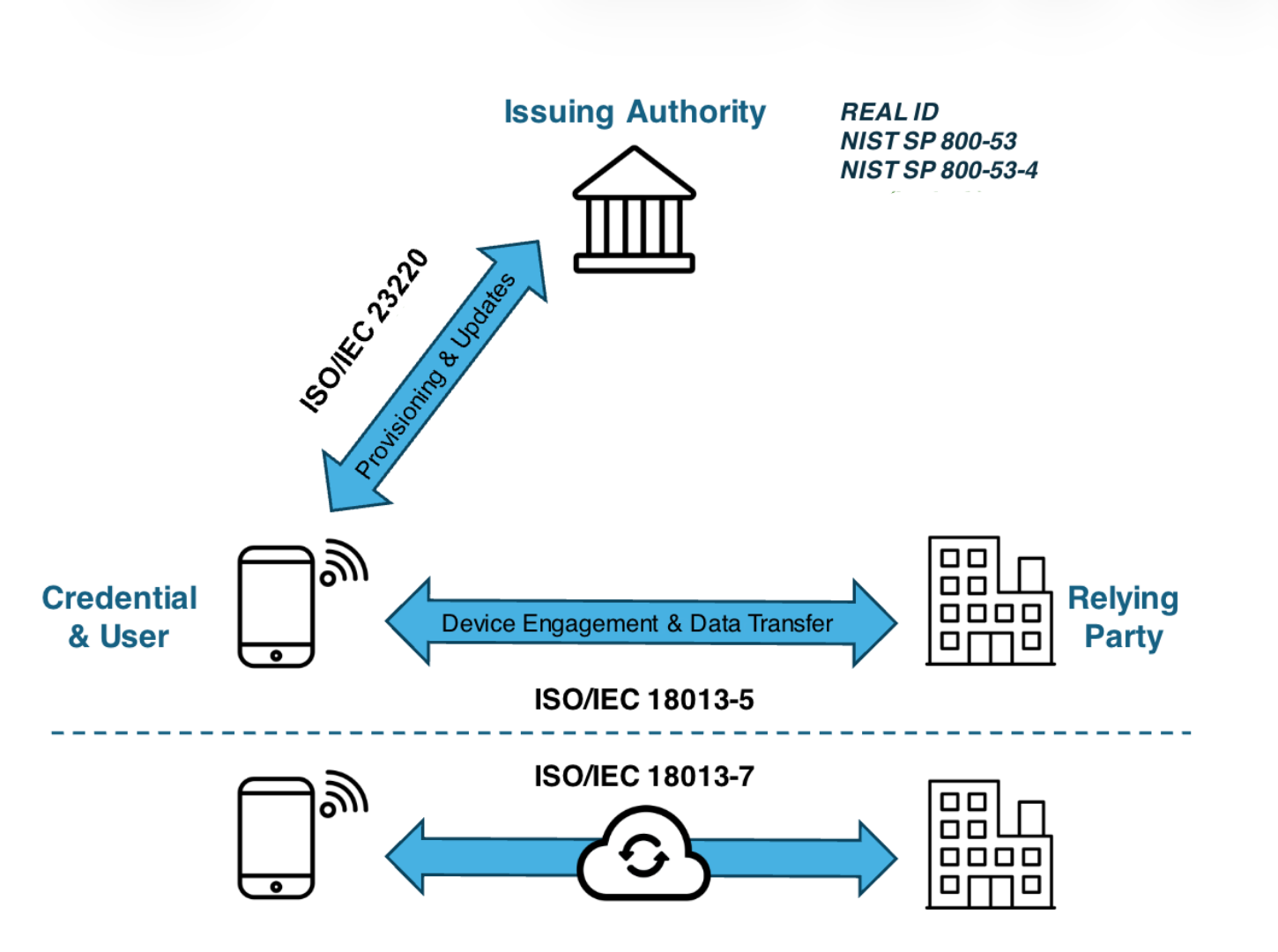
Behind the Tap2iD experience is a three-party trust model. These are the actors that make in-person digital ID verification work.
03
How the trust model connects to the product
04
How does in-person mDL presentation and verification work
07
Which standards sit behind Tap2iD
ℹ️
Management layer
Verify with Credence is the web portal used to configure verifier behavior, manage trust and data profiles, monitor activity, and support deployed verifier endpoints across hardware and SDK-based environments.
- Standard
- ISO/IEC 18013-5
- Name
- Mobile Driving Licence
- What It Governs
- In-person device engagement and data transfer between phone and verifier via NFC, QR, or Bluetooth.
- Standard
- ISO/IEC 23220 (draft)
- Name
- Mobile eID Framework
- What It Governs
- How the issuing authority provisions and updates credentials on the user's device.
- Standard
- ISO/IEC 18013-7 (draft)
- Name
- Online Presentations
- What It Governs
- Extends the mDL standard to remote and online verification through a secure cloud relay.
| Standard | Name | What It Governs |
|---|---|---|
| ISO/IEC 18013-5 | Mobile Driving Licence | In-person device engagement and data transfer between phone and verifier via NFC, QR, or Bluetooth. |
| ISO/IEC 23220 (draft) | Mobile eID Framework | How the issuing authority provisions and updates credentials on the user's device. |
| ISO/IEC 18013-7 (draft) | Online Presentations | Extends the mDL standard to remote and online verification through a secure cloud relay. |